Simplify Security With Penetration Testing as a Service (PTaaS)
Enabling security teams to nearly eliminate critical and high findings within the first six months.
Most penetration testing programs rely on an outdated, point-in-time model. Annual tests, fragmented tools, and manual effort leave teams struggling to keep up as environments change.
Our Penetration Testing as a Service (PTaaS) was built to replace that model with continuous, actionable testing.

Continuously Identify Exposures
Uncover weaknesses across infrastructure, identity, applications, and cloud, as your environment changes.

Validate What Matters
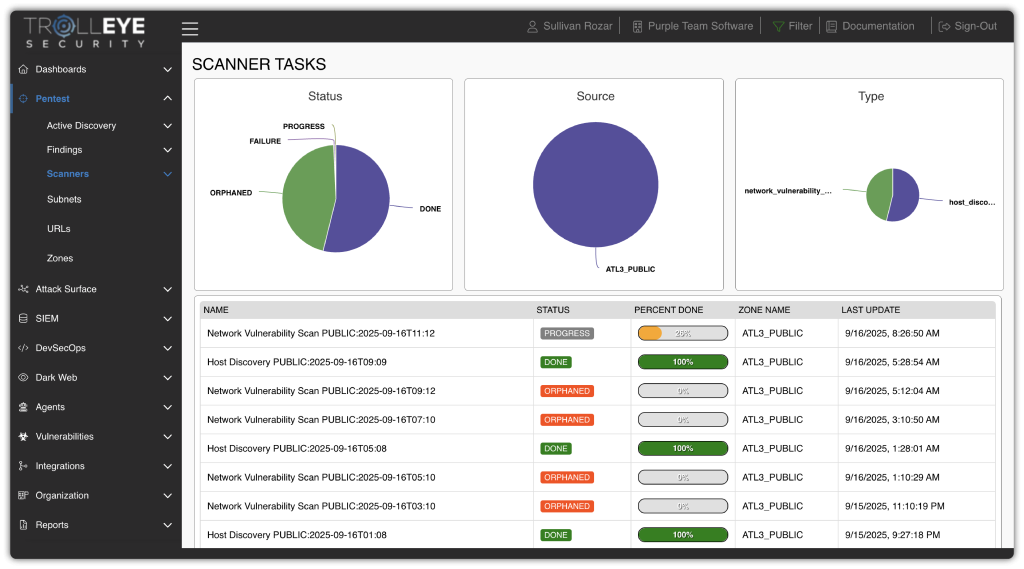
Penetration testing runs continuously, with cadence options from quarterly to weekly, so risks are validated before they become incidents.

Mobilize Remediation
Our team doesn’t just deliver reports, we help prioritize and route findings to the right teams so real risk gets fixed faster.
Strengthen Exposure Management with Penetration Testing as a Service (PTaaS)
Most penetration testing providers focus on identification. Our PTaaS is built to support exposure management, connecting identification, validation, and remediation into a single continuous operating model.
By combining continuous scanning, manual validation, structured remediation workflows, and ongoing partnership, we help teams build a program that systematically reduces exposure, improves coordination, and strengthens security posture over time.
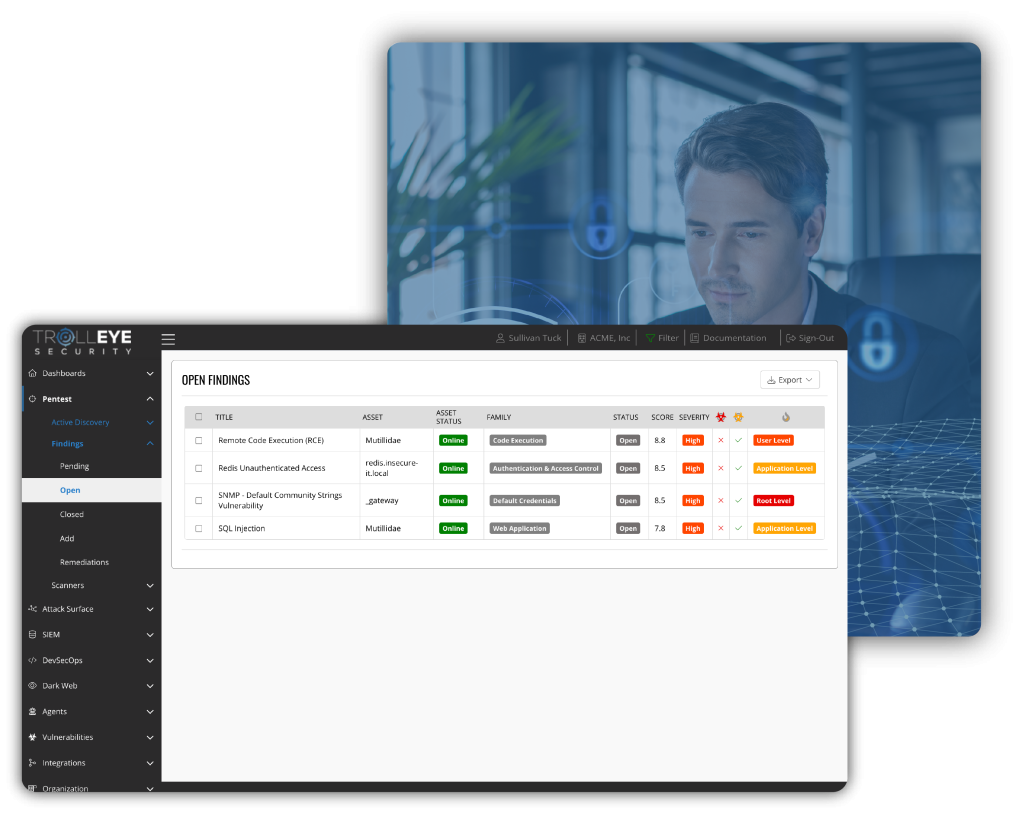
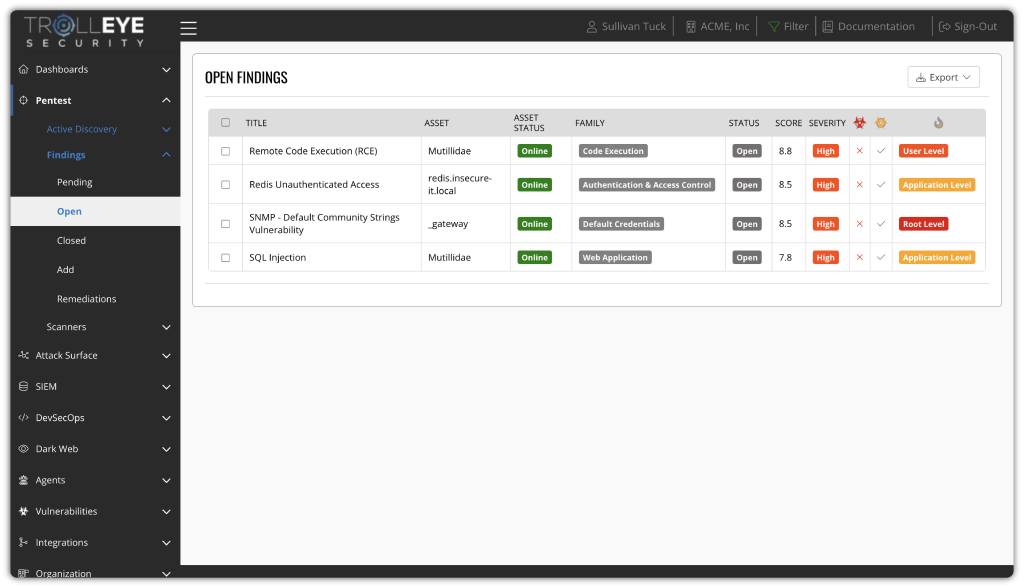
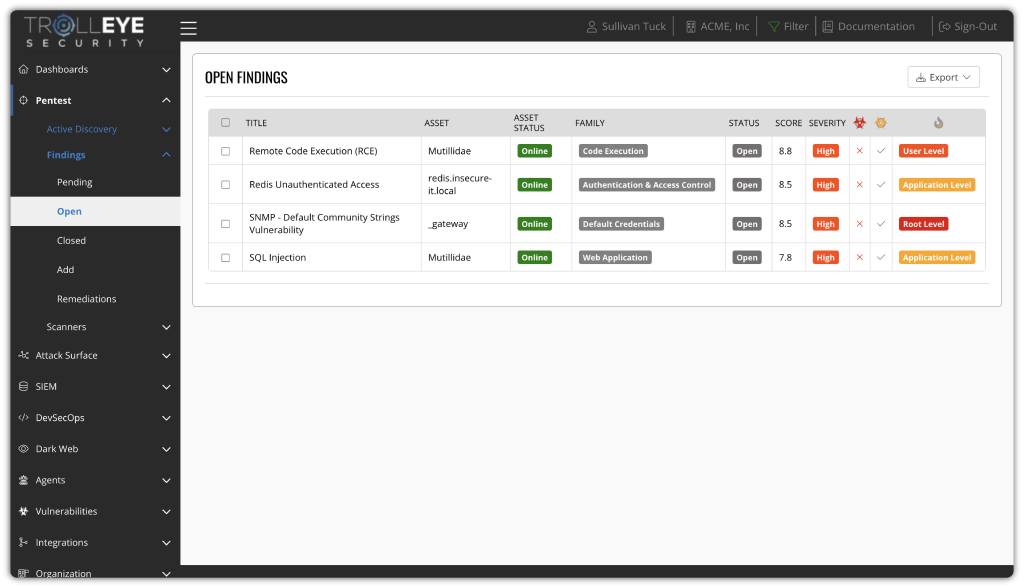
Get The Right Findings To The Right People With Role-Based Task Distribution
Route validated findings directly to the teams responsible through role-based task distribution and integrated workflows. This reduces manual triage, eliminates ownership gaps, and ensures remediation is assigned, tracked, and closed without losing technical or business context.
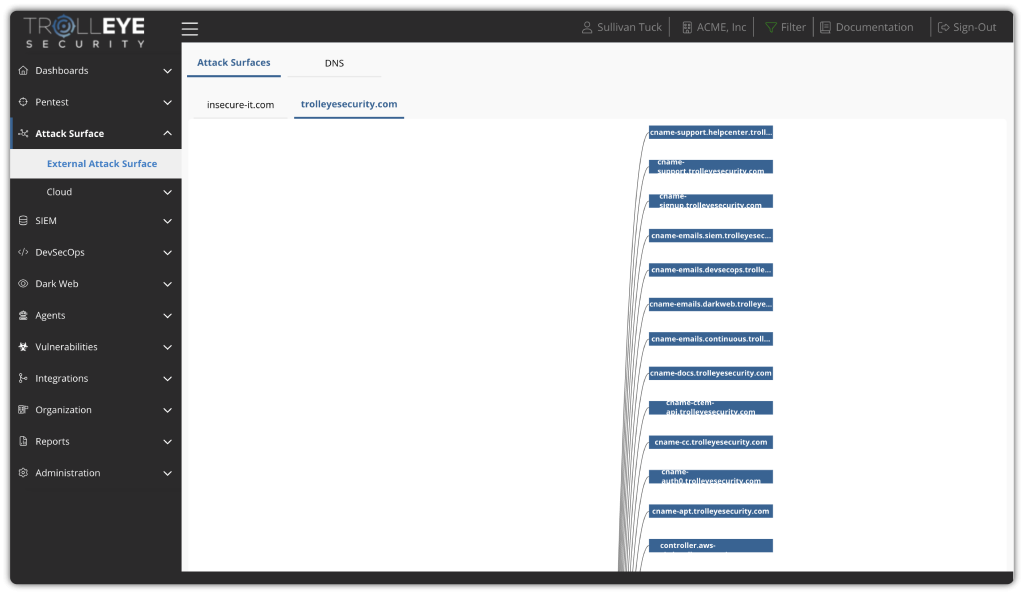
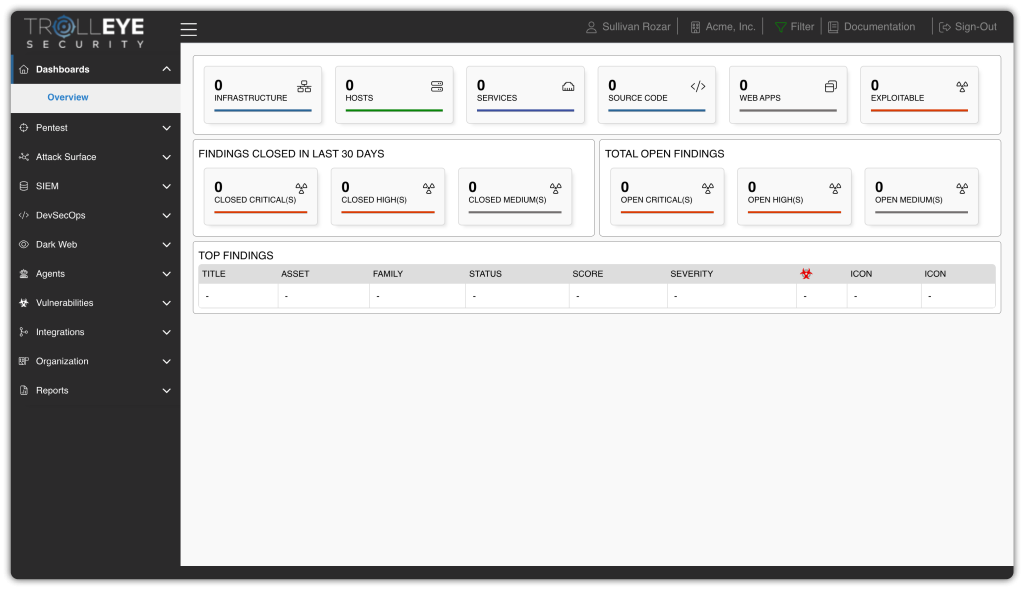
See Your Entire Internal, External, And On-Prem Environment In One Unified View
Maintain continuous visibility across your full internal, external, and on-prem attack surface from a single operational view. By correlating assets, vulnerabilities, and validation, you eliminate blind spots and gain a clear understanding of how exposures connect across your environment.
Test What Actually Puts You At Risk Across Your Entire Attack Surface
Our approach expands testing beyond traditional vulnerabilities to include external attack surface, dark web intelligence, and phishing-based access. By unifying visibility across infrastructure, credentials, and human attack vectors, teams gain a clear view of how risk actually enters the organization, enabling smarter prioritization and faster remediation.
Resolve Issues Through Guided Remediation And Ongoing Support
We don’t just deliver reports, we help you operationalize remediation. Our team works alongside yours to remove recurring issues through remediation guidance, automation, and process improvements that prevent the same exposures from coming back quarter after quarter.
Validate Real-World Risk With Specialized Testing Across The Entire Attack Surface
Go beyond a single assessment type with continuous testing across network, application, and physical security. Our PTaaS program adapts to how your environment actually operates, validating risk across digital and real-world attack paths.
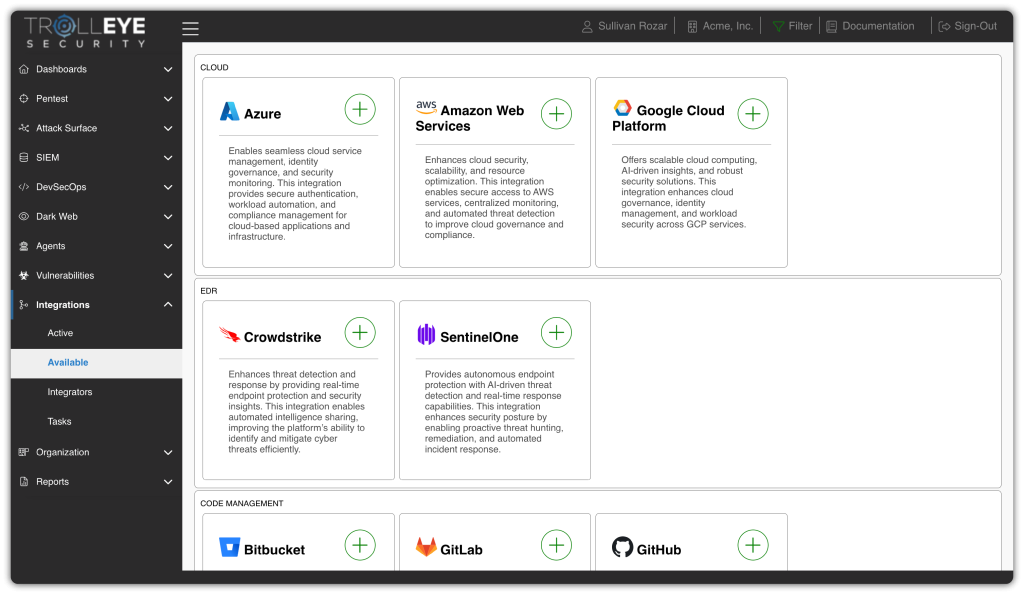
Turn Findings Into Action By Embedding Testing Into Your Existing Stack
Integrate PTaaS directly into your existing security, IT, and development stack, including ticketing, cloud, EDR, and collaboration tools. By embedding findings into the systems your teams already use, you reduce manual effort, eliminate duplicate work, and turn testing results into faster remediation and measurable return on your security investment.

TrollEye Security Recognized as a Sample Vendor in Gartner’s 2025 Hype Cycle for Application Security

TrollEye Security Recognized as a Sample Vendor in Gartner’s 2025 Hype Cycle for Security Operations
Security Leaders on Why They Choose TrollEye Security
“Nothing short of exceptional.” “It’s simple, yet powerful.” “A wonderful addition to our development lifecycle.”
If you’re curious about the experiences of other security leaders with our penetration testing, we invite you to browse through some of our reviews. We build a relationship of trust with our clients, and we’re proud of the work we’ve done to help them secure their organizations.
On average, our clients see critical and high findings drop to almost zero within six months of starting PTaaS.




A PTaaS Process Focused on Mobilization Across Your Entire Attack Surface
Our Penetration Testing as a Service (PTaaS) process is built to support continuous exposure management by helping teams not only identify risk, but also address the root causes that lead to repeat exposure.
Instead of treating testing as a standalone activity, we deliver security as a program, combining a structured process for continuous validation, a centralized platform for mobilizing remediation, and an ongoing partnership focused on improving how security is operationalized across the organization.

Establish Real Visibility Across Your Entire Attack Surface
We begin by continuously identifying and analyzing your internal and external assets across domain, network, application, cloud, identity, and human attack vectors. Automated discovery is combined with manual reconnaissance to build an accurate, real-world view of how your organization is exposed.

Focus Security Effort on What Actually Drives Risk
Findings are enriched with threat context, exploitability, and business impact. Rather than ranking issues based on technical severity alone, we help teams understand which exposures attackers would realistically exploit first, aligning remediation with true operational risk.

Mobilize Teams to Reduce Exposure Faster
Validated findings are operationalized through structured remediation workflows. Issues are assigned based on role, tracked centrally through our platform, and supported by our team to ensure vulnerabilities are eliminated, mitigated, or accepted with clear ownership and accountability.

Continuously Validate That Fixes Are Effective
As remediation occurs, we rescan and retest to confirm issues are resolved and that new exposures haven’t been introduced. This creates a continuous feedback loop that keeps security posture aligned with how your environment actually evolves.

Build a Stronger, More Resilient Security Program Over Time
Each testing cycle feeds into long-term improvement. We analyze exposure trends, remediation performance, and recurring root causes, helping teams refine processes, introduce automation, and mature their security program with every iteration.


Our process enables us to deliver 12x the testing frequency of traditional models, for less than twice the cost. So clients can mobilize to address exposures with full confidence in their investment.
Learn More About Penetration Testing as a Service (PTaaS)
Use our latest resources, from articles to white papers, to learn more about what Penetration Testing as a Service (PTaaS) is, and how it gives your security team the information, tools, and guidance they need to secure your organization.

Download Your Guide to Penetration Testing as a Service (PTaaS)
Learn what true PTaaS is and how it can help your security team reduce risk through continuous scheduled engagements.
Go on the offensive against hackers. Contact TrollEye Security today and get a demo of Penetration Testing as a Service.
Our Essential Penetration Testing Services
We are a full-service penetration testing company, and every engagement is delivered through our Penetration Testing as a Service (PTaaS) model.
Core internal, external, network, IoT, and phishing testing are included, with advanced capabilities such as web application testing, physical testing, and red teaming available as expanded validation options.
Our comprehensive approach covers every major exposure domain, from internet-facing infrastructure and connected devices to identity risk and human-layer vulnerabilities.


Internal Penetration Testing
Simulates an attacker inside your environment to validate privilege escalation paths, lateral movement, and high-impact internal exposures.

External Penetration Testing
Tests internet-facing systems to validate exploitable weaknesses that increase real-world attack surface risk.

Network Penetration Testing
Identifies and validates exploitable weaknesses across network devices, services, and segmentation controls that enable access or pivoting.

IoT Device Penetration Testing
Evaluates connected devices and their ecosystem to uncover vulnerabilities that enable device compromise, data exposure, or network entry.

Web Application Penetration Testing
Simulates real-world attacks against applications to validate business-impacting vulnerabilities in logic, auth, and data handling.

Physical Penetration Testing
Tests physical access controls through controlled attempts to bypass restrictions and identify facility-driven compromise paths.

Attack Surface Management
Continuously identifies and validates internal, external, and on-prem assets to reduce attack surface risk.

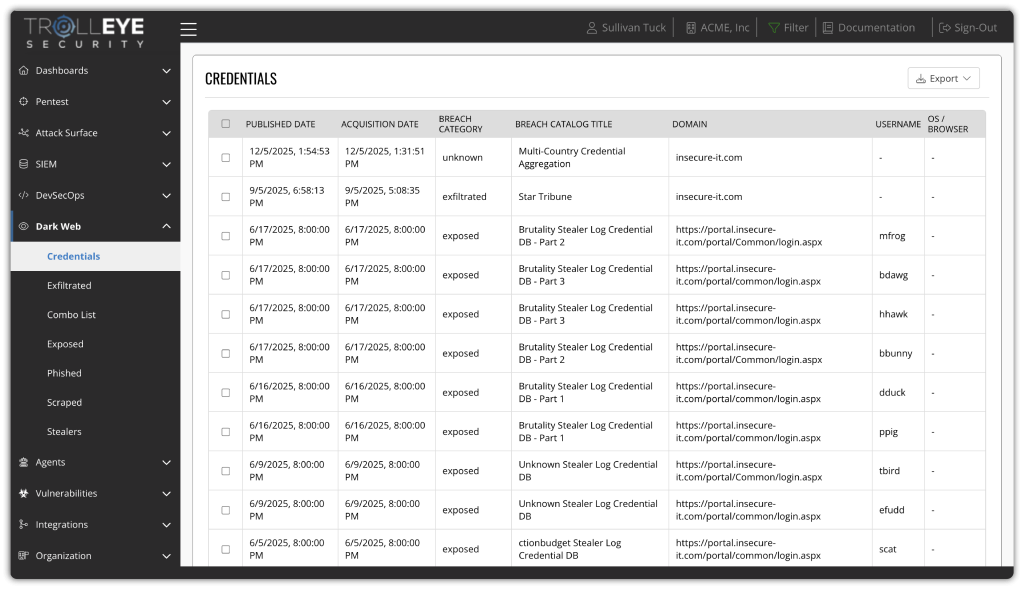
Dark Web Analysis
Continuously validates compromised credentials, executive exposure, and third-party risk to reduce identity-driven attack paths.

Phishing Assessments
Measures employee susceptibility to credential-harvesting campaigns to reduce identity-driven exposure.

Red Teaming Assessments
Simulates advanced adversary behavior across domains to evaluate detection, response, and full-compromise resilience.

Social Engineering Assessments
Tests human-layer defenses via pretexting and impersonation to identify exploitable behavioral gaps.

Incident Response Tabletop Exercises
Runs breach simulations to evaluate decision-making, coordination, and readiness before a real incident occurs.
FAQs
What's Penetration Testing as a Service (PTaaS)?
Penetration Testing as a Service (PTaaS) is a delivery model for penetration testing that emphasizes ongoing testing, scalability, and integration. Instead of a one-time engagement, PTaaS provides continuous and scheduled testing supported by a platform for managing findings and remediation tracking in real time.
What's the difference between PTaaS & traditional penetration testing?
Traditional penetration testing is typically conducted annually or biannually and provides a snapshot of your security posture at a single moment in time. These tests are often compliance-driven, and once the report is delivered, the engagement ends until the next scheduled test.
In contrast, Penetration Testing as a Service (PTaaS) is continuous. Our own PTaaS solution provides regular testing cycles (up to weekly) validated findings delivered in real-time through our platform, and ongoing collaboration with your team to help prioritize remediation. Instead of a one-off project, PTaaS is an ongoing partnership aimed at reducing your real-world risk, not just checking a compliance box.
How often is our penetration testing performed?
By default, our PTaaS includes monthly testing, providing consistent visibility into your organization’s risk posture. For organizations with higher security or compliance requirements, testing frequency can be increased to a weekly engagement as part of our enterprise-grade service.
What types of penetration testing are included?
Our PTaaS solution includes a broad range of testing methods to ensure complete coverage of your environment. These include External Penetration Testing, Internal Penetration Testing, Network Penetration Testing, Web Application Penetration Testing, IoT Device Penetration Testing, and more.
How much does our PTaaS solution cost?
Our Penetration Testing as a Service (PTaaS) starts at $20 per asset a month, with a 100-asset minimum. Our solution includes everything most organizations need to get started with continuous, high-impact testing and analysis, including:
- Monthly penetration testing engagements.
- Attack Surface Management for up to 3 cloud accounts.
- One domain monitored through Dark Web Analysis.
- Quarterly Phishing Assessments with credential validation.
- Regular cadence meetings with our security experts.
From there, the package can be customized based on your environment and security goals, whether you need additional assets, more frequent testing (such as weekly), expanded dark web coverage, or increased attack surface management.
How is TrollEye's PTaaS different than other solutions?
Many PTaaS vendors offer little more than an on-demand scheduling tool or a portal to download static reports. Our PTaaS is built for security outcomes, not just convenience. Here’s what sets us apart:
- True Continuous Penetration Testing: Our testing isn’t on-demand, crowdsourced, or fully automated. We use a blend of automated tools and manual validation, conducted at regularly scheduled intervals, to provide true and continuous penetration testing.
- Regular Cadence Meetings: We meet with your team regularly to review testing results, prioritize remediation, and help improve your processes.
- Streamlined Remediation Management: Through role-based task distribution and a Kanban board interface our platform makes it easy to track, assign, and verify remediation tasks across teams, ensuring nothing slips through the cracks.
- Additional Security Features Included: Our solution includes Attack Surface Management, Dark Web Analysis, and Phishing Assessments to help uncover and reduce more risk across your environment, not just the technical vulnerabilities.
This combination helps reduce critical and high-risk vulnerabilities faster and supports measurable, long-term improvements in your security posture.
Does TrollEye offer other services than PTaaS?
Yes, while PTaaS is our core offering, we provide a full suite of services designed to continuously reduce risk across the attack lifecycle. These include:
- Dark Web Analysis: Identify and validate exposed credentials linked to your organization, assess third-party risk, and monitor executive data exposure.
- DevSecOps as a Service: Secure your development pipeline with continuous code scanning, penetration testing, and a platform that integrates with your entire SDLC.
- Managed SIEM & Purple Teaming: 24/7 detection and response supported by red-blue team collaboration to accelerate threat identification and remediation.
Each service is powered by our own platform and backed by a team of seasoned security professionals who work directly with your internal teams.

Begin Strengthening Your Network Today
Forward-thinking, proactive business owners around the world are turning to Penetration Testing as a Service (PTaaS) as their best bet for minimizing their vulnerability to cyberattacks, maintaining regulatory compliance, and creating an impenetrable network. Stay ahead of the curve - and the hackers - with TrollEye Security on your side.
If you are ready to take your business's cybersecurity to the next level, contact TrollEye Security and ask about our continuous penetration testing services. You’ll be on your way to a stronger, more resilient network.