Continuously Identify and Address Exposures Across Your Attack Surface
Continuous Threat Exposure Management (CTEM) across the exposures that attackers actually target.
Your attack surface changes daily, and one-time testing can’t keep up. That’s why we deliver continuous testing and validation to find and fix exposures before attackers can exploit them.

Reduced Risk
Identify and remediate exposures that pose the greatest threat with continuous discovery, validation, and prioritization across your attack surface.

Integrated Security Operations
Consolidate and connect your stack with capabilities spanning ASM, DAST, SIEM, and more. While integrating across Cloud, EDR, Code Management, and Firewall tools.

Continuous Audit Readiness
Maintain continuous audit readiness with continuous testing, complete remediation logs, and Drata and Vanta integrations that clearly demonstrate compliance.
Your Attack Surface Changes Every Day. Your Testing Should Too.
Many organizations still treat security as a periodic task, a compliance checkbox rather than a continuous effort to uncover real risk. The result is predictable: exposures go unnoticed, remediation slows, and attackers exploit the gaps in between.
At TrollEye Security, we take a continuous approach. Our Continuous Threat Exposure Management (CTEM) services continuously validate exposures across your networks, applications, people, and vendors, while our platform makes remediation faster, clearer, and more efficient.
Supported by a long-term partnership approach, we help your team mature over time, turning ongoing collaboration into measurable security improvement.


Reduced Risk
Continuously identify and validate exposures ranging from technical vulnerabilities to dark web threats.
Secure your attack surface with testing that spans networks, applications, your human firewall, and more.
Mobilize to address the threats that matter most and fix root causes, with expert remediation guidance.

Integrated Security Operations
Reduce costs with a platform that consolidates ASM, DAST, SCA capabilities, and more.
Increase efficiency with a centralized location for managing exposures.
Lower friction with broad integrations, across Cloud, EDR, Code Management, and Firewalls.

Continuous Audit Readiness
Easily meet requirements across SOC 2, HIPAA, and PCI DSS with continuous testing.
Maintain continuous audit readiness with complete testing and remediation logs, reducing manual collection.
Simplify audit prep with Drata and Vanta integrations that clearly show auditors your assessment history.
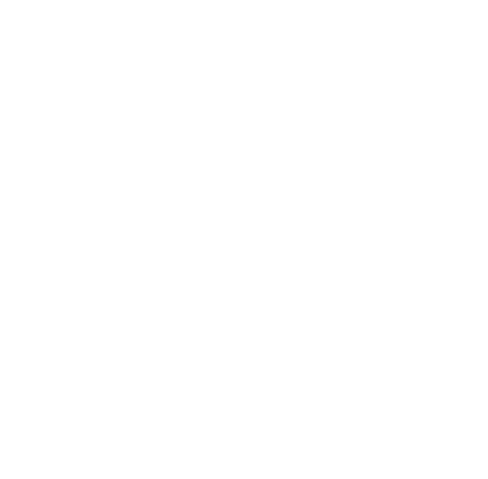
Security Leaders on Why They Choose TrollEye Security
“Nothing short of exceptional.” “It’s simple, yet powerful.” “A wonderful addition to our development lifecycle.”
These are the outcomes security leaders describe after working with TrollEye Security. Behind those results is a continuous exposure management approach that validates real-world risk across the attack surface.
"We selected TrollEye Security for their comprehensive approach to security testing and their expertise in simulating sophisticated threat actors.
TrollEye's approach of employing various attack vectors from dark web analysis to physical breach attempts demonstrated their understanding of the complex nature of modern cybersecurity threats facing financial institutions. It’s simple, yet powerful."


How a Software Company Reduced Vulnerabilities by Over 97% with DevSecOps
Learn how an Atlanta-based software company used DevSecOps to ensure secure releases, reducing overall vulnerabilities by over 97%, and eliminating critical and high findings.

Why General Bank of Canada Chose Our Red Teaming Assessments to Validate Their Security Posture
Learn why a highly regulated, Schedule-1 Canadian bank chose to use TrollEye Security for a red teaming assessment to validate security across network, infrastructure, dark web, and physical attack vectors.
Our Continuous Threat Exposure Management (CTEM) Services
Our CTEM strategy combines the use of our four services to put your defenses to the test and build a program that identifies and reduces the risks that matter most. Each service is built on three key principles;
- Continuous Process - Gain continuous visibility with regular testing against a set of common risks and attack vectors.
- Integrated Platform - Manage every service from our platform, centralizing visibility, streamlining remediation efforts, and consolidating toolsets.
- Partnership Approach - Get expert guidance directly from your security testers with monthly cadence meetings designed to support your needs.
Each one addresses a specific type of exposures that pose a threat to your organization, providing your security team with the continuous visibility and validation needed to ensure security.

Penetration Testing as a Service (PTaaS)
Penetration Testing as a Service (PTaaS) delivers continuous validation of your defenses through up to weekly testing, real-time reporting, and direct collaboration with your security team.
Dark Web Analysis
Dark Web Analysis service uncovers hidden risks by monitoring dark web forums and marketplaces for your compromised credentials, vendor breach records, and executive data exposure.
DevSecOps as a Service
DevSecOps as a Service integrates security directly into your development lifecycle, ensuring vulnerabilities are identified and resolved before code reaches production.
Managed SIEM & Purple Teaming
Managed SIEM & Purple Teaming offering combines continuous monitoring with active adversarial testing to validate and strengthen your detection and response capabilities.
A Unified Platform for Efficient Exposure Management
At the core of our approach is a unified platform that centralizes exposure management and drives measurable risk reduction.
It connects every stage of testing, validation, and remediation in one environment, giving security teams complete visibility and control across their attack surface.
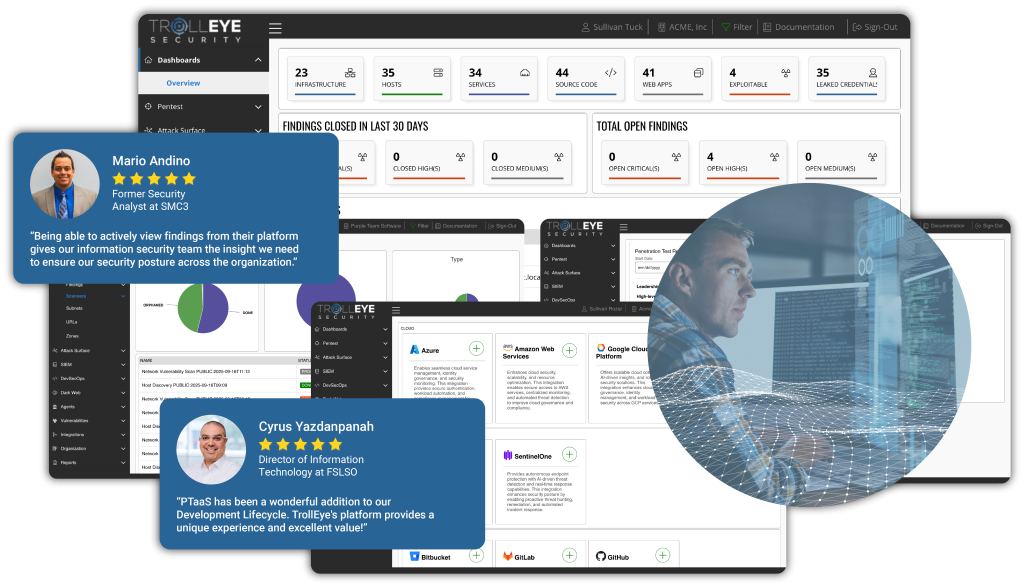
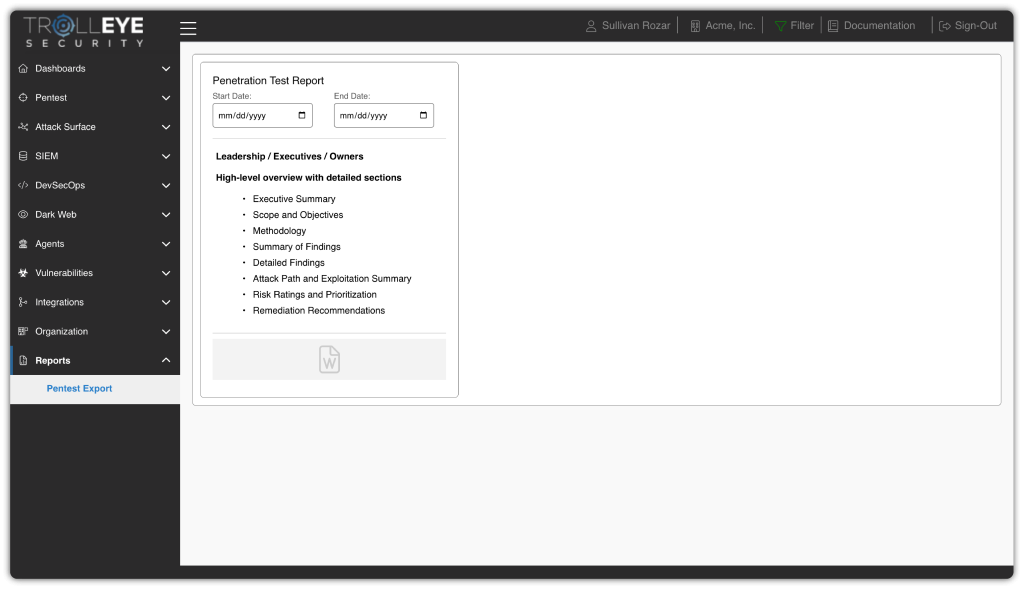
Get the Right Findings to the Right People
Role-based task distribution ensures findings reach the right people with the right context, accelerating remediation and keeping teams focused on meaningful progress.
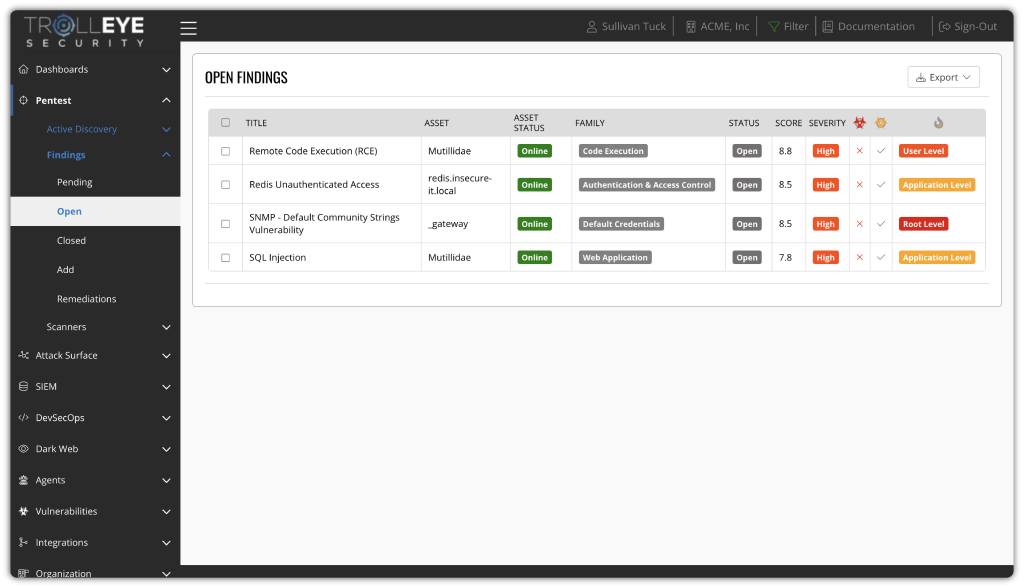
Unify Security Capabilities, Eliminate Fragmentation
By bringing together ASM, SAST, DAST, SCA, Dark Web Monitoring, and SIEM into a single platform, you eliminate tool sprawl and fragmented visibility, enabling unified threat detection, faster validation, and streamlined remediation from one place.

Connect Your Ecosystem Without Disruption
With broad integrations across your existing security and development stack, our platform connects seamlessly with tools like Azure, AWS, Jira, and GitHub to unify visibility and streamline collaboration.
Simplify Audits and Strengthen Accountability
Automated compliance tracking and reporting make it simple to map findings to key frameworks like NIST, ISO, and SOC 2, reducing manual effort and audit fatigue.
Learn More with Our Resources
Use our latest resources, including white papers and case studies, to learn more about how you can use our services to help your security team continuously improve your security posture with the right information, the best tools, and expert guidance.
Download Crowdsourced Cybersecurity vs Penetration Testing as a Service (PTaaS)
Learn about the key differences between Crowdsourced Cybersecurity and PTaaS, including which testing approach is best for you.

Download Your Guide to Penetration Testing as a Service (PTaaS)
Learn what true PTaaS is and how it can help your security team reduce risk through continuous scheduled engagements.

Download Your Guide to Dark Web Analysis
Learn how Dark Web Analysis goes beyond traditional monitoring, and gives your security team insights into stolen credentials, vendor risk, and executive exposure.

Download Your Guide to DevSecOps
Learn how you can integrate security into the entire SDLC through DevSecOps, resulting in your organization producing more secure software, at a faster pace, cost-effectively.
Download Why SIEM Should Include Purple Teaming
Learn why SIEM should include purple teaming, and how your security team can remediate more vulnerabilities and stop more breaches by combining them.

Download Your Guide to Physical Penetration Testing
Learn how you can use physical penetration testing to identify gaps in your physical security, which is one of the most overlooked aspects of most cybersecurity strategies.

Download Enhancing Employee Training With Phishing Assessments
Learn how you can use phishing assessments to identify risks in your human firewall and to improve your training program to reduce successful attacks.
Download What is Continuous Threat Exposure Management (CTEM) And How to Implement It
Discover how to turn Continuous Threat Exposure Management (CTEM) into a measurable, operational reality with our implementation guide today.
Download How Does TrollEye Enable Continuous Threat Exposure Management (CTEM)?
Discover how our process, platform, and partnership work together to turn CTEM into a living, measurable program with our guide to how we enable Continuous Threat Exposure Management (CTEM).
Download The Top Five Dark Web Threats & How to Mitigate Them
Learn about the top five threats shaping today’s cybercrime economy, why traditional dark web monitoring tools fall short, and how to turn dark web intelligence into real defense.
Let TrollEye Security Test Your Strength Before Hackers Do
Initial consultation
We’ll conduct a comprehensive analysis of your needs, networks, and assets to be tested.
MSA and RoE signed
The Master Service Agreement (MSA) and Rules of Engagement (RoE) cover all the details.
Testing and reporting
Threat exposure management begins, making your organization more secure with each engagement.
Hackers on your side
Ethical hackers tell cybercriminals, “Nice try. We already thought of that.”

