You Can’t Fix What You Can’t Connect. Unify Exposure Management.
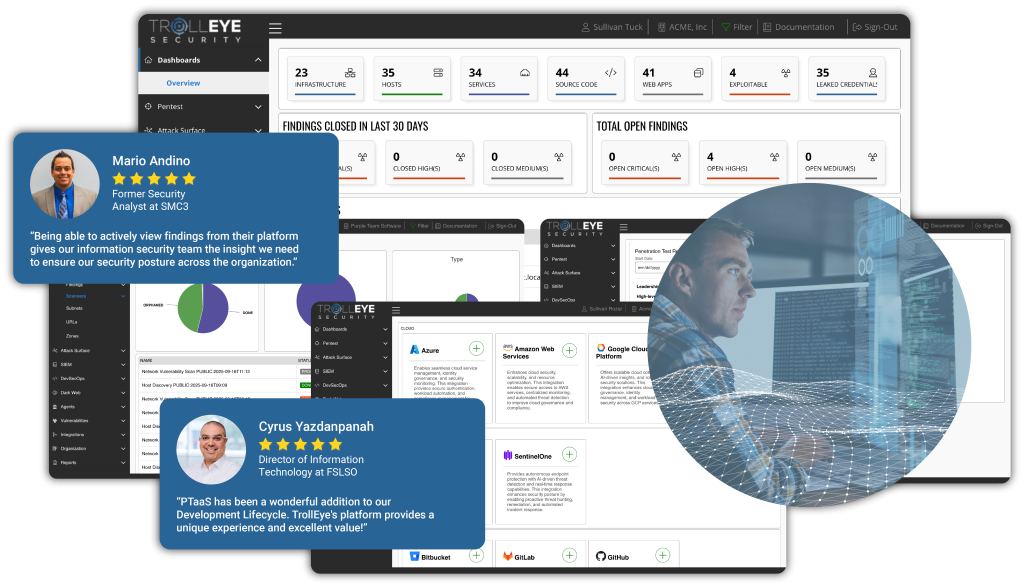
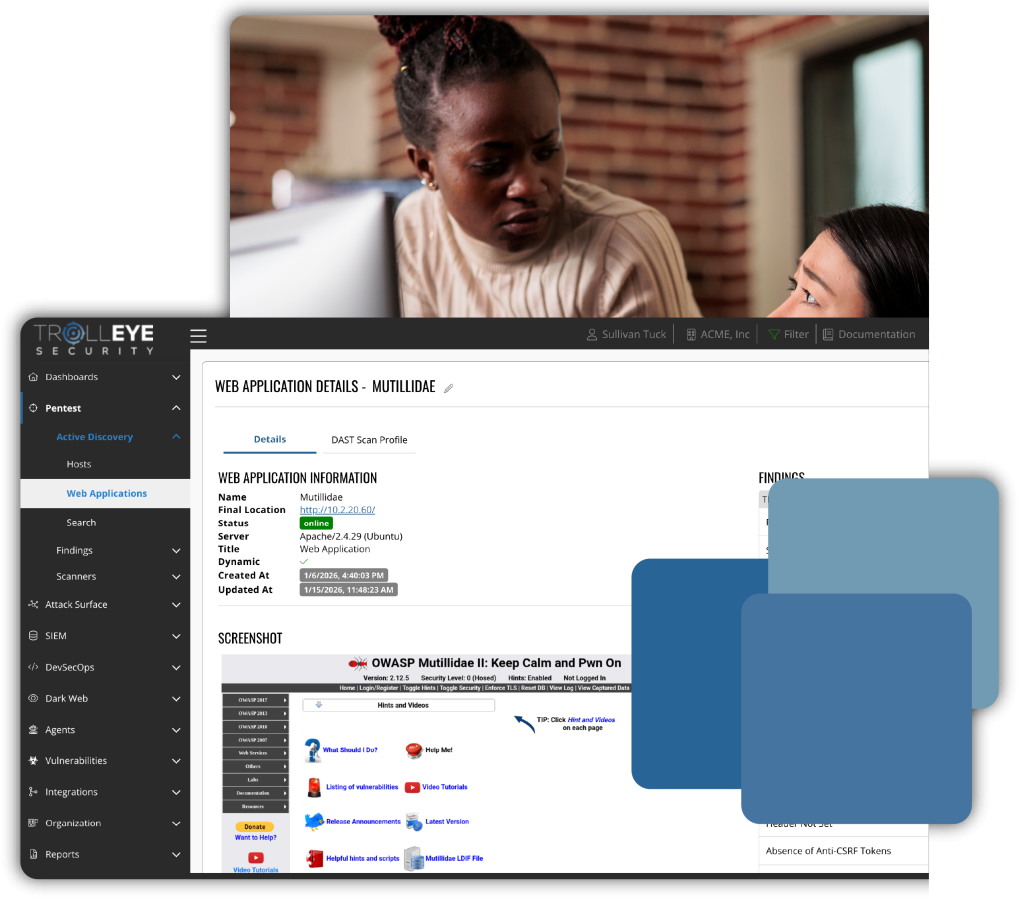
Most organizations still manage exposures through disconnected tools, isolated reports, and fragmented workflows. Our platform changes that with a centralized workspace, giving you a complete view of your attack surface and the ability to manage exposures continuously.

Continuous Discovery
Continuously identify internal and external assets, services, and exposures across your entire attack surface in real time.

Continuous Validation
Validate which exposures represent real-world risk by confirming exploitability through testing, threat context, and security intelligence.

Continuous Prioritization
Correlate findings with asset criticality and business context to route the highest-impact risks to the teams that can actually fix them.
One System for the Identification, Validation, and Remediation of Exposures
Our platform was built to make exposure management seamless, findings from our Threat Exposure Management Services flow into a centralized workspace, where tasks are automatically routed to the right people with the right context.
Integrations across Cloud, EDR, Code Management, and Firewalls keep your existing workflows connected, while full asset histories provide a complete picture of testing, remediation, and progress over time.
It’s everything you need to manage exposures continuously, without the complexity of disconnected systems.
Eliminate Blind Spots Across Your Attack Surface
Maintain a continuously updated view of your internal, external, and cloud environments. As assets change, the platform ensures new systems, services, and exposure points are automatically discovered so nothing critical remains invisible.

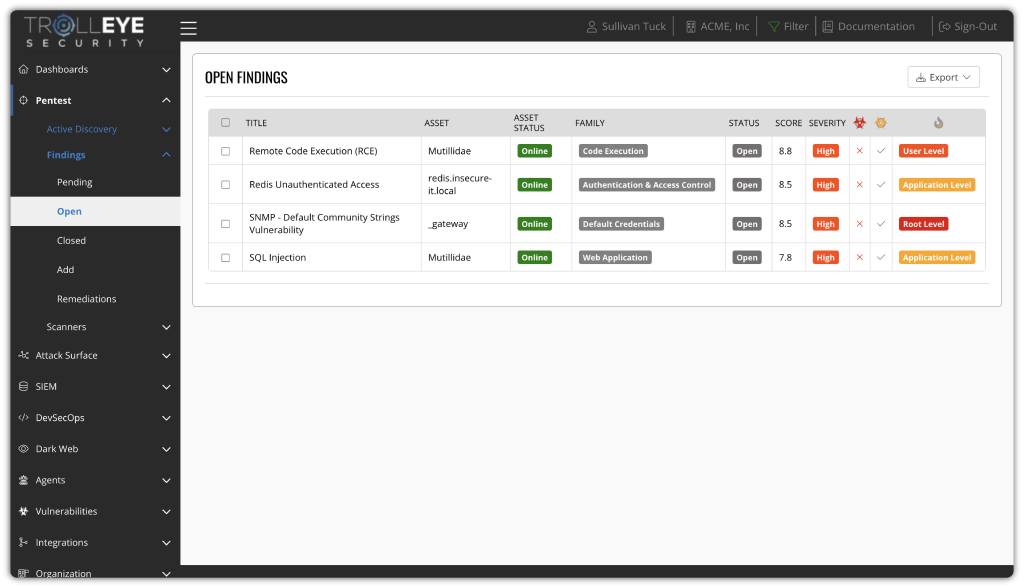
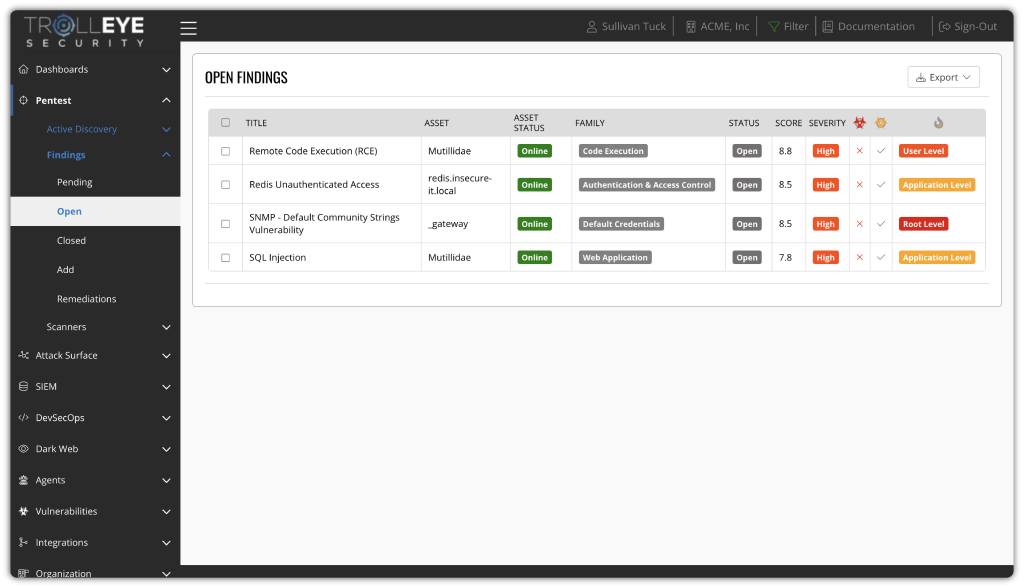
Focus on Real, Exploitable Risk
Move beyond theoretical findings. Exposures are actively validated to determine which issues represent real attack paths in your environment, allowing teams to ignore noise and concentrate on what attackers can actually exploit.

Reduce Exposure Where It Matters Most
Validated risks are prioritized based on real-world impact, exploitability, and business context. This ensures remediation efforts are focused on the exposures that will materially reduce organizational risk, not just improve scan scores.


Mobilize Remediation Across Your Organization
Finding exposures is only half the problem. Real risk reduction happens when validated findings are translated into clear ownership, aligned priorities, and coordinated action across security, IT, engineering, and leadership.
Our platform is built to operationalize remediation, not just report on it.

Get the Right Findings to the Right People with Role-Based Task Distribution
Role-based task distribution ensures findings reach the right people with the right context, accelerating remediation and keeping teams focused on meaningful progress.

Give Teams the Guidance to Fix What Matters Most
Every finding is enriched with technical detail, business impact, asset criticality, and attack path context. Teams see not just what is vulnerable, but why it matters, how it can be exploited, and what reducing that exposure actually achieves.
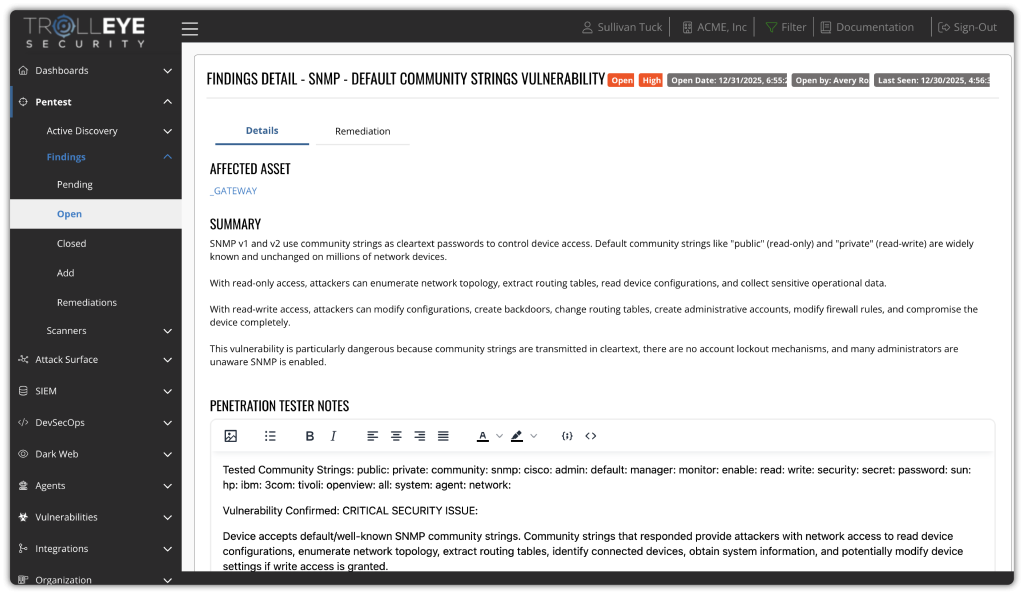
Track and Prove Risk Reduction with Re-Testing and Continuous Validation
Fixes are continuously validated and measured over time, giving security leaders a clear view of what has actually been remediated, what remains exposed, and how overall risk is trending.
Track and Prove Risk Reduction with Re-Testing and Continuous Validation
- SOC Agent - Correlates detection data with real-world exposure to validate threats and reduce alert fatigue.
- Vulnerability Agent - Analyzes scanner results, enriches findings with threat intelligence, and helps prioritize remediation.
- Apex Penetration Testing Agent - Prioritizes exploitable findings and surfaces real attack paths.
Consolidate Exposure Management Across Your Organization
Our platform brings together the security capabilities required to manage exposure across modern environments, including attack surface discovery, application security testing, monitoring, and validation.
By consolidating these functions into a single system, teams gain consistent visibility into real risk and a streamlined way to prioritize and remediate findings.

Ship Secure Code Without Slowing Delivery
Built-in DevSecOps capabilities integrate directly with GitHub and Azure DevOps to identify exploitable weaknesses early in the development lifecycle. Security testing runs alongside development workflows, giving teams fast, actionable feedback that reduces rework, limits production risk, and keeps releases moving.
Maintain Visibility and Control Across Dynamic Cloud Environments
Native integrations with Azure and AWS provide continuous insight into cloud assets, configurations, and exposures. As environments change, security posture updates automatically, helping teams manage risk without relying on periodic reviews or manual inventories.

Unify Network Visibility Across Best-of-Breed Controls
Integrations with Palo Alto and Fortinet bring network telemetry and security signals into a single operational view. This allows teams to correlate network activity with vulnerabilities and attack paths, improving detection accuracy and response speed.

Strengthen Endpoint Defense with Shared Context
CrowdStrike and SentinelOne integrations feed endpoint telemetry directly into the platform, linking device-level activity to broader attack chains. This enables faster investigation, clearer prioritization, and more coordinated response across security teams.

Focus Remediation on What Can Truly Be Exploited
The platform centralizes vulnerability data and ties it to real-world exploitability. By combining scanning results with validation and attacker perspective, teams can prioritize remediation based on actual risk, not theoretical severity scores.

Detect, Validate, and Respond with Context
SIEM, security agents, and penetration testing management work together to surface real threats across the environment. Findings are enriched with validation and attack context, reducing alert fatigue and enabling security teams to focus on incidents that actually matter.

Turn External Exposure Into Actionable Risk Reduction
Attack Surface Management and dark web monitoring continuously track exposed assets, leaked credentials, and third-party risk signals. Instead of reactive alerts, teams get prioritized intelligence tied directly to real attack paths, helping them address threats before they’re exploited.

Integrations That Operationalize Exposure Management
Our platform integrates directly with the systems your teams already use to create a single operational view of exposure across your environment.
By integrating with your existing cloud, development, and security tools, our platform turns fragmented security data into real, prioritized exposure that teams can actually fix.

Azure & Azure DevOps
Ingests cloud asset, identity, and configuration data to maintain real-time visibility into your cloud environment.
Amazon Web Services
Continuously pulls asset and service metadata from AWS to track changes across your cloud attack surface.
CrowdStrike
Ingests endpoint telemetry and threat signals to enrich exposure data with real-world behavioral context.
SentinelOne
Correlates endpoint detection data with vulnerability and exposure findings.
GitHub
Connects directly to code repositories to embed security testing into development workflows.
Azure & Azure DevOps
Ingests cloud asset, identity, and configuration data to maintain real-time visibility into your cloud environment.
Palo Alto Networks
Ingests firewall policies and network telemetry to align exposure findings with actual enforcement controls.
Fortinet
Pulls network security data from Fortinet devices to correlate exposures with real network controls.
Jira
Automatically routes findings to the right teams as actionable tickets, enabling faster remediation and clear ownership.
Vanta
Continuously maps exposures to compliance controls, maintaining audit readiness without manual collection.
Drata
Aligns security data with regulatory requirements, streamlining compliance reporting.
Microsoft Teams
Receive real-time notifications on new findings to keep your team aligned and remediation moving without delays.

Slack
Receive real-time notifications on new findings to keep your team aligned and remediation moving without delays.
Unify, Simplify, and Strengthen Your Exposure Management Program
When every capability operates from a single platform, security stops being a set of isolated tools and becomes a unified strategy. Our platform gives you the visibility to see across every service, the control to manage exposures efficiently, and the confidence that your defenses are always improving.
By connecting every part of your security program into one continuous process, we transform exposure management into measurable, lasting resilience.