Enabling Continuous Threat Exposure Management (CTEM)
From theory to execution, turn CTEM into a functional advantage.
Continuous Threat Exposure Management (CTEM) is quickly becoming the gold standard for modern security programs. But implementing CTEM isn’t just about adopting a new framework, it’s about putting the right people, processes, and technology in place to continuously identify, validate, and reduce exposure across your organization.


“According to Gartner, by 2026 organizations that prioritize their security investments based on a continuous exposure management program will be 3x less likely to suffer a breach.”
What Sets TrollEye Security Apart in Enabling Continuous Threat Exposure Management (CTEM)
Implementing CTEM is not just about tooling or running a few scans. It requires a disciplined process, a collaborative partnership, and a purpose-built platform to consistently reduce threat exposure over time.
At TrollEye Security, we deliver all three. Our continuous approach to testing and validation, our commitment to true partnership with your internal teams, and our purpose-built platform are designed to work in concert, supporting every phase of your CTEM program.
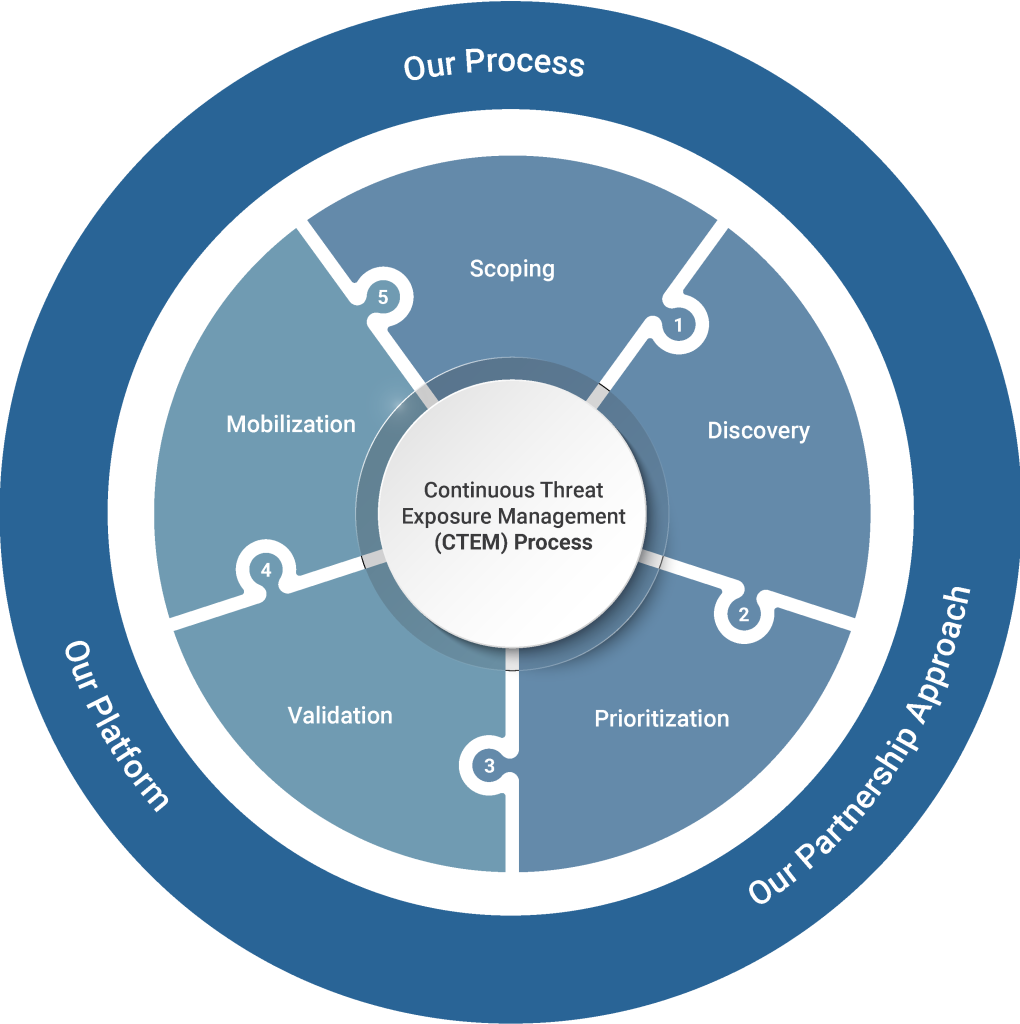
Our Process - Designed for Continuous, Measurable Exposure Reduction
Most security assessments are point-in-time, our process is continuous by design, and focuses on identifying real exposures across your attack surface.
Whether you engage with us for Penetration Testing as a Service (PTaaS), DevSecOps, or Managed SIEM, every offering is structured around ongoing improvement, not just a one-time test. Furthermore, each solution addresses a wide array of threats and attack vectors, giving you visibility into a large range of potential exposures, from network vulnerabilities to vendor breaches.

Our Partnership Approach - Built to Support Long Term Improvement
CTEM only works when you have proper guidance on what to exposures to address and how to do it effectively. That’s why we don’t operate as a black-box vendor, we act as an extension of your team. From the first onboarding session to every cadence meeting, our team collaborates closely with your security to provide remediation guidance, help implement automation, and improve your processes over time.
With our partnership focus, we help you mobilize and truly reduce risk over time, enabling truly continuous exposure management.

Our Platform - Purpose-Built for CTEM
Technology is only effective if it helps you take action. Our platform helps make CTEM practical and scalable. It combines testing data, threat insights, and remediation workflows into one centralized location where you can assign tasks based on role, and track progress through a Kanban interface.
With our platform you’re not just collecting findings, you’re acting on them, and you have full visibility into every step of the process, from detection to resolution.

What is Continuous Threat Exposure Management (CTEM)?
Continuous Threat Exposure Management (CTEM) is a structured framework designed to reduce cyber risk by focusing on continuously identifying, validating, and addressing exposures across your attack surface. These exposures range from technical vulnerabilities in your systems and applications, to broader threats like compromised credentials and cloud misconfigurations.
It follows a five-stage lifecycle (scoping, discovery, prioritization, validation, and mobilization) designed to align security efforts with the threats that pose the biggest risk and business impact.
Get Started With Continuous Threat Exposure Management (CTEM) Today, Using TrollEye Security’s Unique Approach
How We Power Every Stage of Your CTEM Program
Executing proper CTEM takes more than just tools, and that’s where TrollEye Security comes in. Our process, partnership model, and platform are designed to support and accelerate every phase of the CTEM lifecycle.
Here’s how we fit into every stage of your program, from scoping to mobilization and everything in between.

CTEM Step #1 - Scoping
The first step in any exposure management program is defining the scope, deciding which systems, applications, users, and business functions are mission-critical, and what level of risk is acceptable across them. This requires close collaboration between technical and business stakeholders to ensure the right assets are targeted for assessment.
We support this step in the initial scoping phase of starting our services, where you specify what assets are to be tested and what exposures are to be monitored for.
Key Questions We Help Answer in Step #1
What does my universe look like?
What assets do I know about?
What assets don’t I know about?
What are my “crown jewels”?
Are my assets visible?

CTEM Step #2 - Discovery
Once the scope is defined, discovery involves building a complete and dynamic inventory of your digital footprint, including internet-facing systems, third-party dependencies, cloud workloads, source code, and credentials that may have been exposed through leaks or misconfigurations. This step surfaces both known and previously unseen assets that attackers could exploit.
We support this step with our platform which helps identifies and maps out a large number of exposures from misconfigurations in your internal, external, cloud, and on-prem assets, to stolen credentials and vendor risks.
Key Questions We Help Answer in Step #2
Do I have vulnerabilities, misconfigurations, and weaknesses?
What security controls exist?
Are my assets reachable?
Are my assets vulnerable?
Are there threats against them?

CTEM Step #3 - Prioritization
Discovery often reveals hundreds or thousands of potential issues, but not all exposures carry the same weight, prioritization involves mapping these findings to real-world risk by factoring in business context, exploitability, threat actor behavior, and likelihood of attack. This enables security teams to focus on the vulnerabilities that are most likely to be used in an actual breach.
Our platform provides detailed descriptions of each finding, allowing your team to prioritize exposures based on real risk. Furthermore, our experts work with your security team to provide guidance on poses the most risk to your organization.
Key Questions We Help Answer in Step #3
Am I exposed? How exposed?
Are my security controls optimized?
What is my prioritized exposure risk?
How should I disposition my risks?

CTEM Step #4 - Validation
Prioritized findings must be validated to confirm whether they’re truly exploitable and to assess how well existing controls perform under pressure, this step moves beyond theoretical risk and into practical impact. Validation involves safe, controlled exploitation techniques and adversary emulation to determine if alerts are triggered, response processes activate, and containment is achieved.
We support regular validation through continuous testing and analysis of your security posture, constantly identifying exploitable vulnerabilities, actionable credentials, risky vendors, insecure source code, and much more.
Key Questions We Help Answer in Step #4
Am I truly susceptible to attack?
Are identified exposures real?
Are my exposures exploitable?
Can my security controls defend me?
Can I detect a breach?
Would an attack succeed?
Which key business processes are at risk?
What are the potential business impacts?

CTEM Step #5 - Mobilization
Validated findings only improve your security posture if they lead to meaningful action, mobilization turns insight into execution by assigning ownership, driving remediation workflows, and ensuring accountability at both the technical and executive levels. This includes setting timelines, integrating with ticketing systems, and tracking progress toward closure and measurable risk reduction.
We help your team mobilize efficiently through our platform, which enables easy remediation management through role-based task distribution and a Kanban board interface. Furthermore, with regular cadence meetings our security experts provide remediation guidance and help your team improve your processes, supporting long term improvement.
Key Questions We Help Answer in Step #5
What possible actions are feasible?
What are optimal responses?
How should I prioritize actions?

FAQs
What makes CTEM different from traditional vulnerability management?
Traditional vulnerability management often focuses on periodic scans and static risk scoring. CTEM goes further by continuously discovering exposures, validating them through real-world testing, and tracking remediation progress to ensure true risk reduction over time.
Do I need specific tools to implement CTEM?
CTEM isn’t just about tools, it’s about process. While the right platform can support CTEM, successful implementation depends on a disciplined lifecycle approach, effective collaboration, and integration into day-to-day operations.
How long does it take to see results from CTEM?
Many organizations begin seeing measurable improvements in visibility, prioritization, and remediation within the first 90 days. Over time, CTEM compounds these gains by creating a culture of continuous improvement.
Is CTEM only for large enterprises?
No, while CTEM is especially valuable in complex environments, organizations of any size can adopt the framework. The key is aligning the scope and cadence of activities to your risk profile and business priorities.
Turning Exposure Management Into Measurable Security Improvement
Continuous Threat Exposure Management isn’t just a framework, it’s a discipline that demands coordination, visibility, and action across every phase of the exposure lifecycle. At TrollEye Security, we help you operationalize CTEM by combining expert-led services, an integrated platform, and a partnership mindset that keeps your goals front and center.
If you’re ready to make exposure management continuous, measurable, and outcome-driven, reach out to our team today.


