Threat Modeling: Frameworks, Practices, and Daily Integration
In today’s cyber landscape, attackers aren’t waiting until you’re ready; they’re continuously scanning, probing, and exploiting weaknesses the moment they appear. Organizations can’t afford to play defense reactively. They need structured ways to anticipate threats before they materialize. That’s where threat modeling comes in.
Threat modeling is the practice of systematically identifying potential threats, analyzing how they might be exploited, and prioritizing defenses accordingly. Whether you’re securing a new application, reviewing an infrastructure change, or strengthening your overall risk management strategy, frameworks exist to provide the structure and consistency you need.
Table of Contents
Why Organizations Need Threat Modeling
Cybersecurity budgets are finite, but the threats are endless. Without a structured approach, organizations often waste resources chasing low-impact vulnerabilities while overlooking high-risk exposures. Threat modeling helps solve this by providing a proactive blueprint for defense, helping teams prioritize what truly matters.
One of the main advantages is anticipation. Instead of waiting for a penetration test or an incident to reveal weaknesses, threat modeling highlights potential attack paths early, whether in code, system design, or business processes. By surfacing these risks upfront, teams can address them at a fraction of the cost compared to retroactive fixes.
A SecurityCompass survey found that 62% of organizations believe their threat modeling capabilities prevent over 70% of high-risk vulnerabilities, with 99% saying it prevents over 50%.
- The 2023 State of Threat Modeling by SecurityCompass
Threat modeling also bridges the gap between technical and business priorities. A vulnerability in a minor application might not demand immediate remediation, but a similar weakness in a system that stores customer data could lead to financial loss, regulatory fines, and reputational damage. Frameworks like PASTA explicitly connect technical threats with business risks, helping ensure that security decisions align with organizational goals.
Finally, threat modeling fosters a culture of continuous security. When integrated into daily operations, such as during software sprints, infrastructure updates, or incident response reviews, it moves beyond a one-off exercise and becomes a core part of how teams design, build, and manage secure systems. Over time, this consistent application reduces attack surfaces and builds resilience.
Key Threat Modeling Frameworks
Several well-established frameworks guide how organizations structure their threat modeling. Each brings a unique perspective, making them more or less suitable depending on your environment, objectives, and maturity level.
STRIDE: Spoofing, Tampering, Repudiation, Information Disclosure, Denial of Service, and Elevation of Privilege
Developed by Microsoft, STRIDE is one of the most widely used frameworks. It categorizes threats into six buckets: Spoofing, Tampering, Repudiation, Information Disclosure, Denial of Service, and Elevation of Privilege. STRIDE excels in software and application development environments because it provides a checklist-like lens for engineers and architects to spot common risks as systems are designed. Its limitation, however, is that it doesn’t inherently prioritize threats; it identifies categories, leaving teams to assess business impact separately.
DREAD: Damage, Reproducibility, Exploitability, Affected Users, and Discoverability
DREAD is a scoring system designed to measure and compare risk levels of identified threats. It stands for Damage, Reproducibility, Exploitability, Affected Users, and Discoverability. By assigning numerical values across these categories, teams can quantify which risks need immediate action. While DREAD is useful for prioritization, its subjectivity can introduce inconsistency unless organizations standardize scoring criteria across teams.
PASTA: Process for Attack Simulation and Threat Analysis
PASTA, which stands for Process for Attack Simulation and Threat Analysis, is a risk-centric methodology built around seven stages, from defining business objectives to simulating attacks. Its strength lies in aligning security activities with business impact, ensuring that technical threats are always viewed through the lens of potential organizational harm. PASTA is especially effective in enterprises with regulatory or financial exposure, but it requires time and cross-functional collaboration to execute properly.
VAST: Visual, Agile, and Simple Threat Nodeling
VAST, or Visual, Agile, and Simple Threat Modeling, was designed to scale. Instead of relying on abstract lists or scoring systems, it emphasizes automation and integration with agile and DevOps workflows. Using diagrams and models, VAST makes it easier for diverse stakeholders to understand threats and mitigation strategies. Its advantage is in large organizations that need consistent modeling across many applications or systems, though its effectiveness depends heavily on tooling support.
Trike
Trike approaches threat modeling with a focus on risk management and assurance. It defines acceptable risk levels up front, then models threats against those boundaries. Unlike STRIDE or DREAD, which highlight possible attacks, Trike explicitly ties everything back to risk tolerance, making it useful for organizations with strong governance or compliance requirements. However, it can be less intuitive for teams unfamiliar with formal risk management practices.
Each framework offers a different balance between technical depth, business alignment, and scalability. Many organizations adopt a hybrid approach, using STRIDE during design reviews, applying DREAD for prioritization, and leaning on PASTA or Trike for higher-level risk assessments.
"By adopting effective methods, processes, and frameworks, organizations can enhance their security posture and protect their assets from cyberattacks. STRIDE, DREAD, OCTAVE, data flow diagrams, attack trees, and risk assessments are valuable resources for threat modeling, while tools like Microsoft Threat Modeling Tool, OWASP Application Threat Modeling, and the NIST Cybersecurity Framework offer practical solutions. It is essential to continually update and refine threat models to stay one step ahead of cyber adversaries.
Remember, effective threat modeling is not just about identifying threats; it's about building a robust and resilient cybersecurity strategy."

How to Use Threat Modeling Frameworks Effectively
Selecting a framework is only the first step. The real value comes from how consistently and thoughtfully it’s applied. Regardless of which approach you choose, the process generally follows a few common stages:
- #1 – Define the Scope: Start by clarifying what you are modeling. This might be a single application, a network architecture, or even a business process. Scope determines the boundaries of your threat analysis, ensuring you don’t waste time evaluating areas that aren’t relevant to the system at hand.
- #2 – Decompose the System: Break down the target into components, data flows, and trust boundaries. For applications, this could mean diagramming APIs, authentication flows, and storage points. For infrastructure, it might involve mapping connections between cloud services, endpoints, and critical assets. This decomposition makes threats easier to identify and categorize.
- #3 – Identify Potential Threats: Apply the framework’s categories to the system. For STRIDE, you’d walk through each threat type against the decomposed components. For PASTA, you’d consider attacker motivations and simulate realistic attack paths. The framework provides structure, but the team’s expertise is what surfaces practical scenarios.
- #4 – Assess Risk and Prioritize: Not every threat deserves equal attention. Use frameworks like DREAD or Trike to evaluate severity, reproducibility, and business impact. This step ensures remediation efforts focus on the exposures that could cause the greatest harm if exploited.
- #5 – Plan Mitigations: Document the controls, safeguards, or design changes that reduce or eliminate the identified threats. This might mean stronger authentication, input validation, segmentation, or monitoring. The goal isn’t just to fix today’s vulnerabilities but to build in resilience against future attacks.
- #6 – Validate and Iterate: Threat modeling isn’t a one-and-done exercise. Systems evolve, new threats emerge, and controls can fail. Regularly revisiting models ensures they stay current and useful. Many organizations tie threat modeling into code review cycles, infrastructure changes, or quarterly security reviews to maintain relevance.
When applied this way, frameworks stop being academic checklists and become practical tools. They give teams a repeatable, structured approach to thinking like an attacker while aligning security decisions with business goals.
Threat Modeling Example - Cryptocurrency Wallet & Exchange
To see how these frameworks apply in practice, consider the example below, modeling a simplified cryptocurrency ecosystem. Users interact with the Electrum wallet through a GUI, browser, or mobile app, while trading activity flows through an exchange that includes a web front end, backend services, APIs, and databases.
The wallet stores private keys and connects to the blockchain through ElectrumX servers, and a trading bot communicates with the exchange API to automate activity. By mapping these components and their connections, the model highlights where attackers might focus their efforts, such as at trust boundaries between the wallet, exchange, and blockchain.
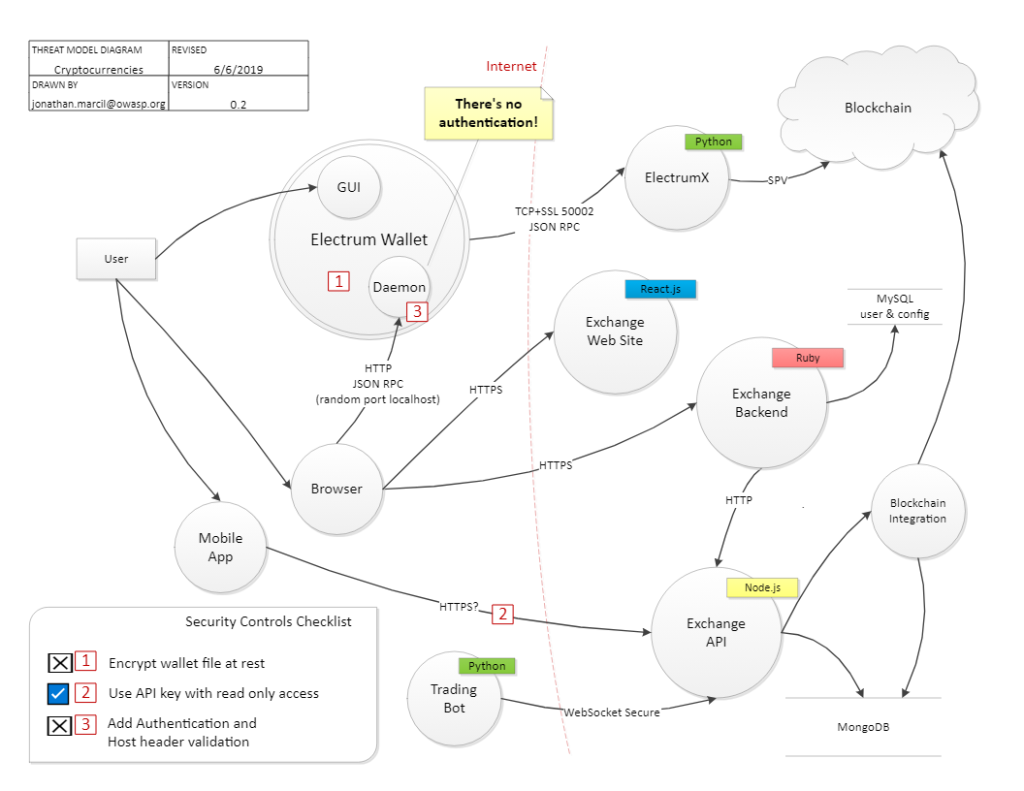
The diagram surfaces several high-impact threats that frameworks like STRIDE help identify: a wallet that isn’t encrypted at rest, APIs exposed without proper authentication or host header validation, unclear transport security between the mobile app and exchange, and backend services dependent on sensitive stored credentials.
While the model shows one control implemented, API keys limited to read-only access, it also makes clear that critical protections like encryption and strong authentication remain missing. This example illustrates how threat modeling moves beyond theory by pinpointing weaknesses early in design, before attackers can exploit them.
With that understanding, organizations can then look to supporting tools that make the process repeatable, collaborative, and scalable.
Top Five Threat Modeling Tools
As threat modeling becomes a more integral part of modern security programs, a growing ecosystem of tools has emerged to help organizations structure the process, streamline analysis, and make threat modeling scalable. While methodologies provide the framework, these tools put structure into practice. Here are five of the most widely used:
IriusRisk is one of the most recognized platforms for automating threat modeling. It provides libraries of known threats, design patterns, and countermeasures that can be applied early in the software development lifecycle. With built-in reporting, integrations with CI/CD pipelines, and a focus on traceability, IriusRisk helps teams shift left and build security into applications from the start.
Microsoft’s free tool has long been a go-to option for teams adopting threat modeling. It’s based on the STRIDE methodology and allows users to create data flow diagrams (DFDs) of applications and automatically identify associated threats. While it is more manual and less customizable than commercial options, it provides an accessible starting point for teams new to structured threat modeling.
Threat Dragon is an open-source project under the OWASP umbrella, available as both a desktop and web application. It supports diagramming of system components, STRIDE analysis, and simple reporting. Because it’s open-source, organizations can adapt and extend it to their needs, making it a flexible option for teams that value transparency and community support.
ThreatModeler emphasizes scalability and enterprise adoption, offering centralized threat libraries, integration with DevOps workflows, and role-based collaboration features. It helps connect security requirements with business risk, aligning well with frameworks like PASTA. ThreatModeler’s focus on automation and repeatability makes it a strong choice for large organizations looking to standardize threat modeling across multiple teams.
SD Elements automates the translation of security and compliance requirements into developer tasks, integrating directly into agile and DevOps workflows. It bridges the gap between regulations and code, helping teams address threats consistently across projects. With its focus on scalability and governance, SD Elements is well-suited for enterprises that need repeatable, risk-based security practices.
While each of these tools has different strengths, they share a common goal: helping organizations proactively identify threats and align security priorities with business objectives. The choice depends on scale, budget, and integration needs, but adopting any of these solutions can significantly reduce blind spots and improve resilience; however, tools alone aren’t enough to manage an effective threat modeling program.
The Top Mistake in Threat Modeling
The most common mistake organizations make is treating threat modeling as a one-time event. Too often, teams conduct a workshop at the start of a project, document the findings, and never revisit them. This static approach quickly loses value because systems evolve, new integrations are added, and attacker techniques change constantly.
Threat modeling only delivers real security benefits when it’s treated as a living process. Embedding it into design reviews, DevOps pipelines, and periodic risk assessments ensures that it adapts alongside the environment. The takeaway: threat modeling is not a report; it’s an ongoing discipline.
Turning Threat Modeling Into a Continuous Discipline
Threat modeling is more than a security exercise; it’s a way of thinking that shifts organizations from reactive defense to proactive resilience. Frameworks like STRIDE, DREAD, PASTA, VAST, and Trike provide structure, but their real value comes from consistent, thoughtful application. When integrated into design reviews, development pipelines, and risk assessments, threat modeling helps security teams anticipate attack paths, prioritize remediation, and align defenses with business objectives.
Traditional defenses can’t anticipate evolving threats. Threat modeling gives you the structure to stay ahead, and by embedding it in our DevSecOps solution, we turn it into a living, continuous discipline that reduces risk across every release.
FAQs About Threat Modeling
What is threat modeling?
Threat modeling is the process of systematically identifying where systems, applications, or processes might be vulnerable to attack. It involves breaking down a system into its components, mapping how data flows, and then examining those touchpoints through the lens of an attacker. The outcome is a clear picture of potential threats and a prioritized plan to address them before they become real-world problems.
Which threat modeling framework should my organization use?
It depends on your goals and maturity. STRIDE is widely used for application security; DREAD helps prioritize risks; PASTA connects technical threats to business impact; VAST scales for large enterprises; and Trike emphasizes risk management. Many organizations adopt a hybrid approach, using different frameworks at different stages of the lifecycle.
How often should threat modeling be performed?
Threat modeling should not be a one-off exercise. It should be revisited whenever systems change, new code releases, infrastructure updates, or integrations occur, as well as during periodic reviews. Leading organizations embed it into DevOps pipelines and quarterly risk assessments.
Do I need special tools to do threat modeling?
Not necessarily. Threat modeling can start with whiteboards, diagrams, or spreadsheets. However, tools like IriusRisk, Microsoft Threat Modeling Tool, and others streamline the process, provide automation, and integrate with CI/CD pipelines, making ongoing application much easier.
How does threat modeling fit into DevSecOps?
Threat modeling complements DevSecOps by “shifting security left”, embedding security considerations earlier in the development process. By integrating into design sprints, CI/CD workflows, and code reviews, it ensures vulnerabilities are caught early, when fixes are cheaper and faster.
Can small organizations benefit from threat modeling, or is it only for enterprises?
Threat modeling benefits organizations of all sizes. Smaller teams may start with lightweight frameworks like STRIDE and simple tools, gaining early insights into critical risks. Larger enterprises often adopt more comprehensive or automated approaches, but the core value, anticipating threats before they’re exploited, applies universally.








